
For any non-product related queries, please write to info@perfios.com.
For any non-product related queries, please write to info@perfios.com.
In the wake of the COVID-19-induced lockdowns, the surge in digital payment methods has undeniably transformed the financial landscape, providing unparalleled convenience to consumers. However, amidst the adoption of digital transactions, a darker reality has emerged – a playground for fraudsters seeking to exploit vulnerabilities and deceive unsuspecting customers.
The ramifications of bank fraud are far-reaching, encompassing not only severe consequences for consumers but also posing significant threats to the integrity of financial institutions. For established entities, the stakes are high, with reputation hanging in the balance and the specter of regulatory non-compliance looming.
In this article, we delve into the intricate web of digital transactions, exploring the vulnerabilities that expose both consumers and institutions to fraudulent activities. Moreover, we'll unravel the strategic avenues through which technology serves as a formidable ally to protect against fraud risk.
But first…
A staggering 51% of organizations, as revealed by a recent PwC study, admit to grappling with fraud within the past two years.
In the domain of lending, fraud risk is the intentional process manipulation, misrepresentation, and falsification of facts—both internally and externally; the consequence arising out of such scenarios is an ominous threat of financial and reputational losses.
That’s where fraud risk management comes in, bringing forward frameworks designed to identify, mitigate, prevent, and control the subtle threats posed by fraudulent activities. In the world of banking and lending, where public funds are entrusted to borrowers, the stakes can be monumental. Neglecting fraud risk directly translates to a menacing impact on both financial stability and reputation.
At the heart of any robust fraud risk management governance framework lie pivotal elements:
1. Definition of bank-level policies and rules governing fraud risk management
2. Rigorous guidelines for the identification, reporting, and continuous monitoring of fraud.
3. Formulation and implementation of process controls strategically engineered for fraud mitigation.
4. Cultivation of fraud risk awareness among internal and external stakeholders.
5. Establishment of policies governing the fraud investigation process.
6. Ongoing pursuit of continuous improvement measures dedicated to fraud prevention and control.
Now, as we delve deeper, let's talk about types of fraud, fraud detection, and control measures within the realms of retail and SME lending.
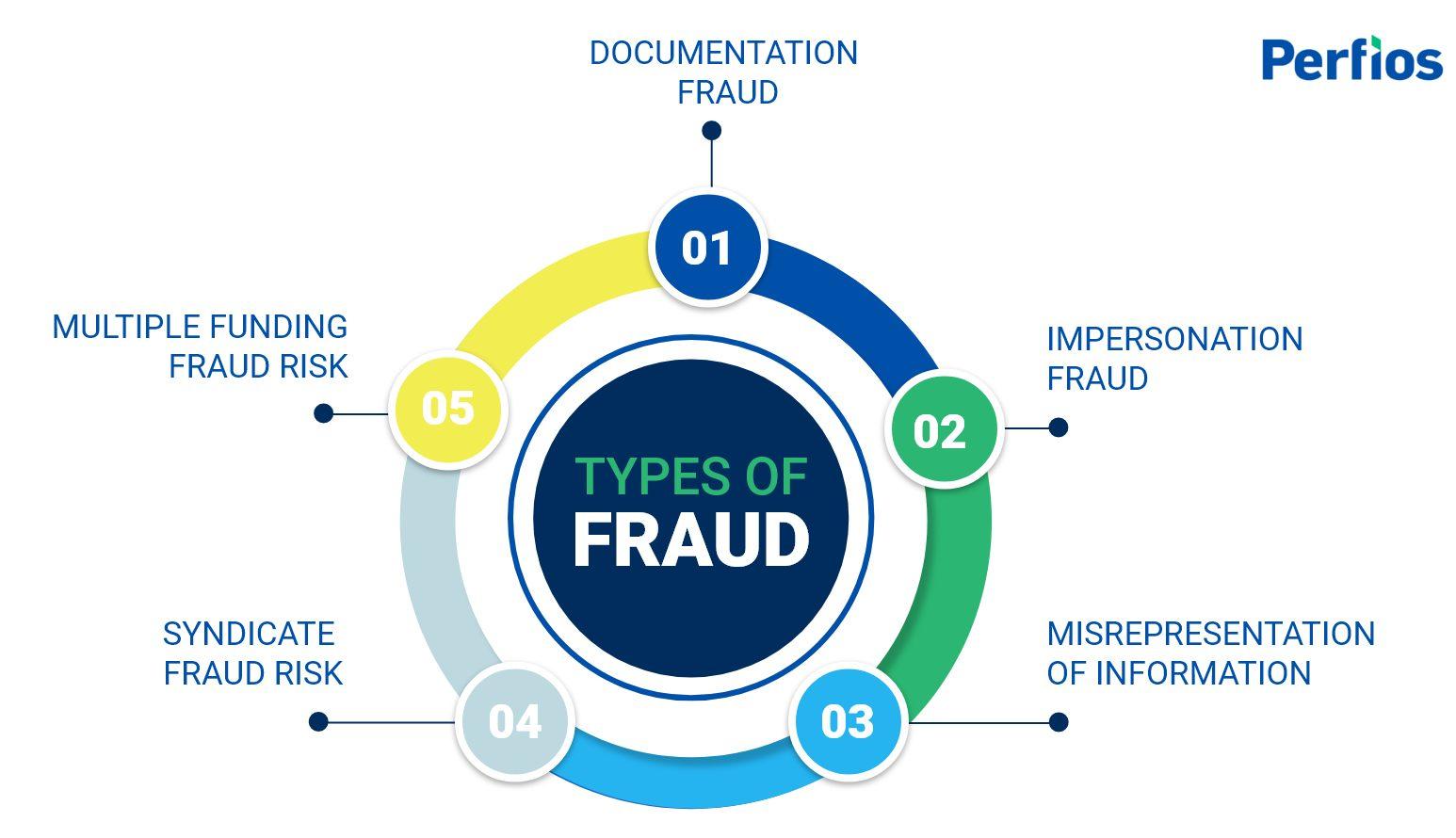
In the domain of lending, the risk of documentation fraud is quite a serious one. This scenario unfolds when crucial documents in the lending process are tampered with or manipulated. The documents can span various types such as KYC, Income documents, Bank statements, Financial statements, and more.
This deceptive practice poses a significant risk, but there are technology frameworks that can assist against protection from documentation fraud. Document tamper detection engines play a crucial role, equipped with the intelligence to identify alterations within presented documents. Techniques like detecting information mismatches and triangulating data across multiple documents further enhance the arsenal against this risk.
Impersonation fraud unfolds in a scenario where genuine customer documents are tampered with for fraudulently availing loan facilities. This deceptive practice involves compromising the identity of a customer, allowing an imposter to illicitly access services on behalf of the legitimate borrower.
To counter such instances of fraud, essential mitigating techniques come into play:
1. Digital Validations and Verifications: Rigorous checks conducted at the digital source ensure the authenticity of customer documents.
2. Multi-Factor Authentication: Implementing additional layers of authentication safeguards the loan application process, requiring multiple forms of verification for added security.
3. Live Location-Based Verifications: Utilizing real-time location data adds a dynamic element to the verification process, enhancing the accuracy and security of customer identity confirmation.
4. Cross Analysis of Information with Intelligence: Employing an intelligence-driven approach involves scrutinizing data for patterns and anomalies, providing insights to detect and prevent fraudulent activities.
In the realm of lending, misrepresentation of information poses another fraud risk challenge. Misrepresentation of information occurs in scenarios where facts are manipulated to hide the true nature of a borrower or their representing firm.
Consider scenarios where borrowers conceal multiple PANs, obscuring crucial details about their credit histories or business records. Similarly, envision business entities seeking lending facilities while strategically omitting essential information about past ventures or unfavorable loan obligations. Picture another entity applying for a bank guarantee, securing a business order entirely different from its usual line of operations.
To counter these deceptive practices, we can employ intelligent, rules-based risk assessment and cross-matching information across various data sources or even AI/ML techniques. These techniques serve as crucial tools, peeling away layers of misrepresentation and ensuring a thorough evaluation of the borrower's genuine financial standing.
Syndicate fraud involves a collaboration of multiple individuals or entities orchestrating fraudulent scenarios to exploit credit services. In retail lending, a deceptive practice unfolds when a company fabricates itself as a legitimate entity, establishing salary and current accounts with banks. Operating under the guise of genuine business transactions, the company will start to engage in seemingly authentic activities, such as salary payments. Exploiting this loophole, individuals wrongfully avail of multiple loan facilities which leads to financial loss of public money.
In another scenario, a real estate builder colludes with multiple individual borrowers to secure individual home loans for purchasing units in their projects. The loans are then distributed among these individuals. However, the projects are abandoned midway, leaving the loans in jeopardy and resulting in substantial losses.
Fraud Detection Techniques: To counter such frauds, employing rules-based intelligence during loan processing and activating relevant fraud alerts emerges as a practical approach. These techniques serve as proactive measures, enhancing the detection and prevention of syndicate fraud.
Even when documents, business transactions, and borrower credentials appear genuine, some borrowers engage in deceptive practices i.e., falsely obtaining multiple fundings against the same underlying documents, transactions, or collateral. This intentional act can lead to overleveraging or leave lenders without adequate collateral coverage, resulting in substantial losses.
Consider a scenario where a borrower secures an unsecured loan from one lender and, within a day or two, obtains similar funding from another source, leading to overleveraged and potential losses for both lenders. The absence of near-real-time information exchange among lenders exacerbates the situation, intensifying the risk of financial losses.
Another prevalent scenario involves borrowers or entities seeking loan facilities against collateral, property, or vehicles that are already financed. This jeopardizes collateral coverage and exposes lenders to potential losses.
To mitigate these risks, it becomes crucial for lenders to have mechanisms in place for near-real-time information sharing.
Navigating the complex terrain of fraud risk reveals diverse threats—from documentation fraud to syndicate collaboration. In response to these challenges, Perfios introduces InteGREAT—an advanced end-to-end loan lifecycle management platform. InteGREAT's unique low-code design addresses multiparty use cases, providing a proactive defense against fraud with features like intelligent alerts, Intelligent validations, and digital disbursements. Empowering clients in diverse financial sectors, InteGREAT stands as a groundbreaking solution for secure, efficient loan management and fraud prevention.
Explore the transformative capabilities of InteGREAT today. For a personalized demonstration and to discover how our platform can elevate your fraud risk management strategies, reach out to us!
Perfios Software Solutions is India’s largest SaaS-based B2B fintech software company enabling 900+ FIs to take informed decisions in real-time. Headquartered in mumbai, India, Perfios specializes in real-time credit decisioning, analytics, onboarding automation, due diligence, monitoring, litigation automation, and more.
Perfios’ core data platform has been built to aggregate and analyze both structured and unstructured data and provide vertical solutions combining both consented and public data for the BFSI space catering to their stringent Scale Performance, Security, and other SLA requirements.
You can write to us at connect@perfios.com
For more Such information contact us@ https://solutions.perfios.com/request-for-demo